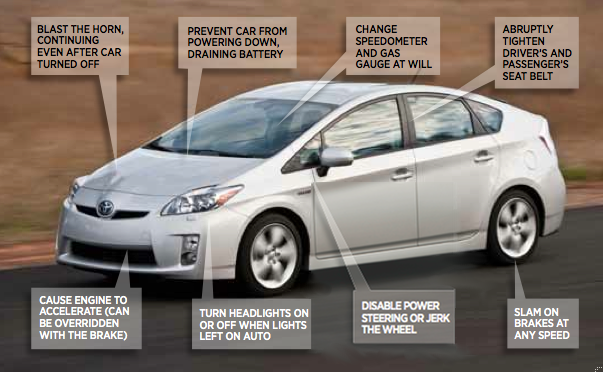
Forbes has a rather alarming article about all the fun ways two researchers (funded by DARPA) have found to hack your car:
As I drove their vehicles for more than an hour, Miller and Valasek showed that they’ve reverse-engineered enough of the software of the Escape and the Toyota Prius (both the 2010 model) to demonstrate a range of nasty surprises: everything from annoyances like uncontrollably blasting the horn to serious hazards like slamming on the Prius’ brakes at high speeds. They sent commands from their laptops that killed power steering, spoofed the GPS and made pathological liars out of speedometers and odometers. Finally they directed me out to a country road, where Valasek showed that he could violently jerk the Prius’ steering at any speed, threatening to send us into a cornfield or a head-on collision. “Imagine you’re driving down a highway at 80 ,” Valasek says. “You’re going into the car next to you or into oncoming traffic. That’s going to be bad times.”
The response from car companies has been to basically say: “We’re not interested in any hack that requires physical access to the car.” That’s a nice thought, and all these hacks did require physically jacking into the car’s computer systems, but the reality is that wirelessly hacking into a car is old news. You can do it ” using the car’s OnStar-like cellular connection, Bluetooth bugs, a rogue Android app that synched with the car’s network from the driver’s smartphone or even a malicious audio file on a CD in the car’s stereo system.”
Valasek (one of the researchers) said simply: “Academics have shown you can get remote code execution. We showed you can do a lot of crazy things once you’re inside.”
So, who’s got the most recent updates, firewall turned on, and updated virus definitions for their car?
See, that’s why I drive a Mac.
Had to share this :)
http://www.theatlantic.com/technology/archive/2013/08/it-now-appears-possible-to-hack-a-fancy-japanese-toilet/278322/
Something has truly gone wrong with the world when your toilet can be hacked…